Researchers Discover A Method To Avoid Vulnerability Detection In Malicious NPM Libraries
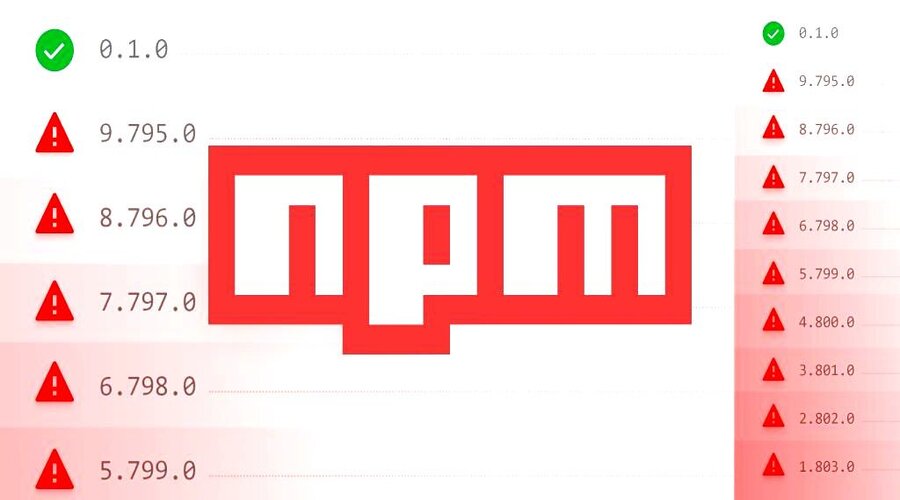
An “unexpected behavior” in the npm command line interface (CLI) tool allows malware that targets the npm ecosystem to evade security checks, according to recent research from cybersecurity firm JFrog.
The install and audit commands of the npm CLI have the ability to check a package and all of its dependencies for known vulnerabilities. By highlighting the flaws, these built-in capabilities serve as a warning system for developers.
However, as JFrog demonstrated, when the packages adhere to specific version formats, the security advisories are not displayed, creating a scenario where critical flaws could be introduced into their systems either directly or via the package’s dependencies.
In particular, the issue only occurs when the installed package version includes a hyphen (for example, 1.2.3-a), which is added to indicate a beta version of an npm module.
Despite the fact that the project maintainers view the discrepancy between regular npm package versions and pre-release versions as an intended functionality, it also makes it vulnerable to abuse by attackers looking to undermine the open-source ecosystem.
Also Read,
Japanese Central Bank Becomes More Hawkish As Inflationary Pressures Prevail; Asian Markets Tumble
“Threat actors could exploit this behavior by intentionally planting vulnerable or malicious code in their innocent-looking packages which will be included by other developers due to valuable functionality or as a mistake due to infection techniques such as typosquatting or dependency confusion,” Or Peles said.
To put it another way, an adversary could release a package in the pre-release version format that appears to be benign, which could then be picked up by other developers who might not be informed that the package is malicious despite evidence to the contrary.
The development serves as a reminder of how the software supply chain is constructed as a network of trust relationships between different parties and how a breach in one link can have an impact on all applications that use the downstream rogue third-party dependency.
Developers are advised against installing npm packages with a pre-release version to guard against such threats unless the source is known to be 100 percent trustworthy.
Also Read,